Exporting and importing the trusted zone
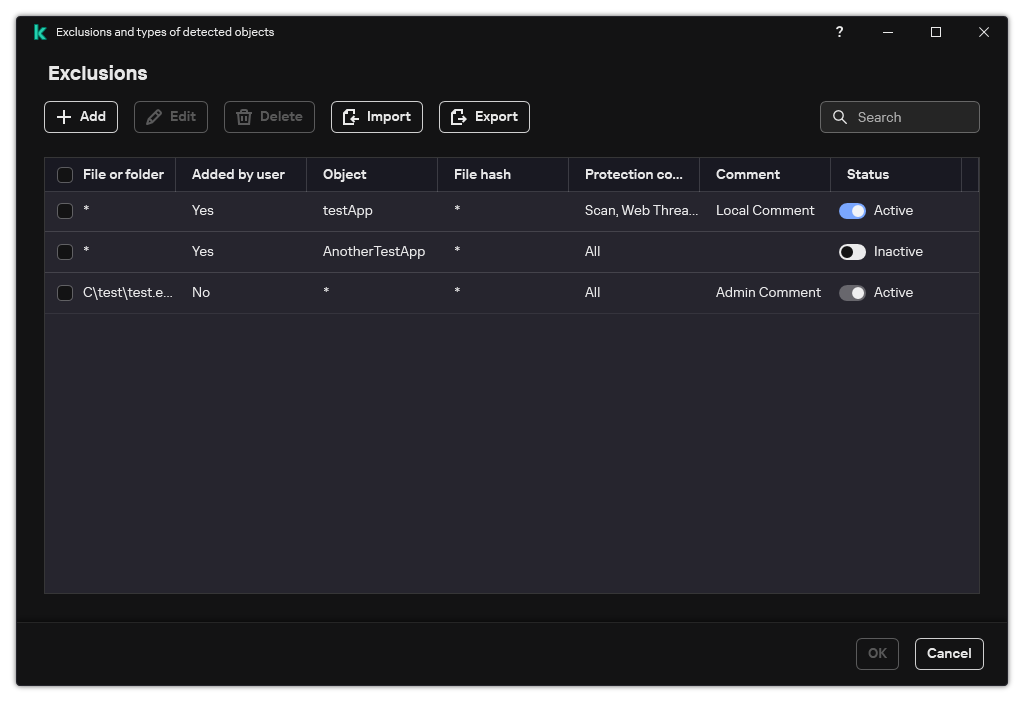
A trusted zone is a system administrator-configured list of objects and applications that Kaspersky Endpoint Security does not monitor when active. The trusted zone consists of the following lists: scan exclusions and trusted applications. You can export these lists to XML files and other formats. Then you can modify the file to, for example, add a large number of exclusions of the same type. You can also use the export/import function to back up the list of exclusions and the list of trusted applications, or to migrate the lists to a different server.
The application uses the following formats for exporting and importing the list of exclusions:
- XML is available in Administration Console (MMC), Web Console, and Cloud Console.
- DAT is available only for import in the Administration Console (MMC). The purpose of this format is to maintain compatibility with older versions of the application. You can convert a DAT file to XML in the Administration Console (MMC) to migrate exclusion lists to Web Console.
- CSV is only available in the local interface of the application.
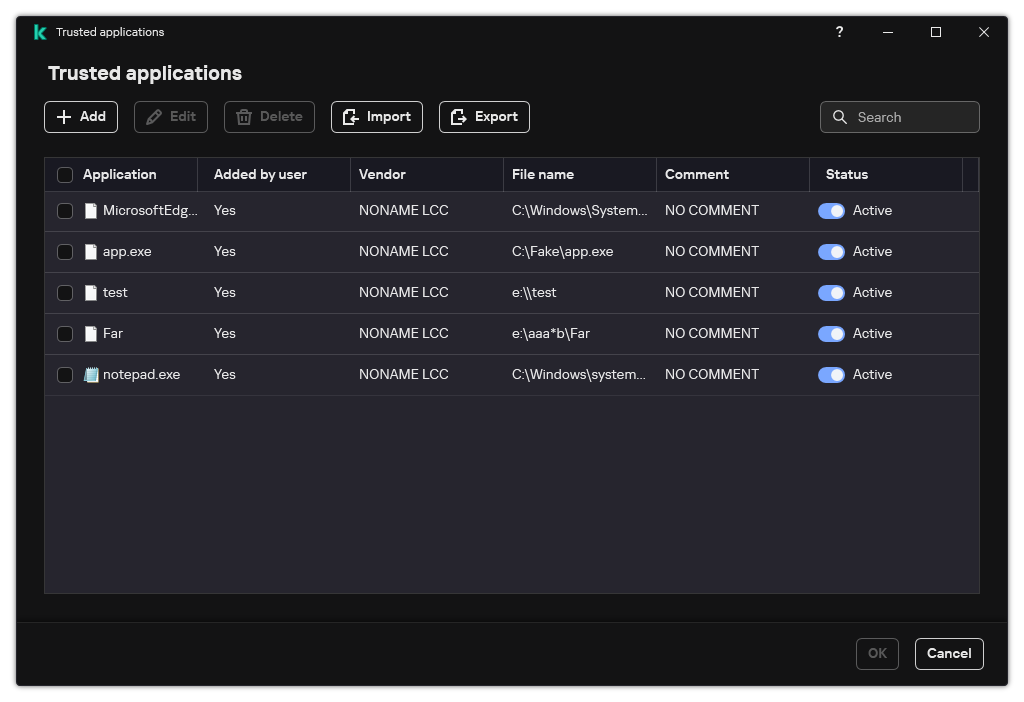
Kaspersky Endpoint Security uses the XML format for exporting and importing the list of trusted applications.
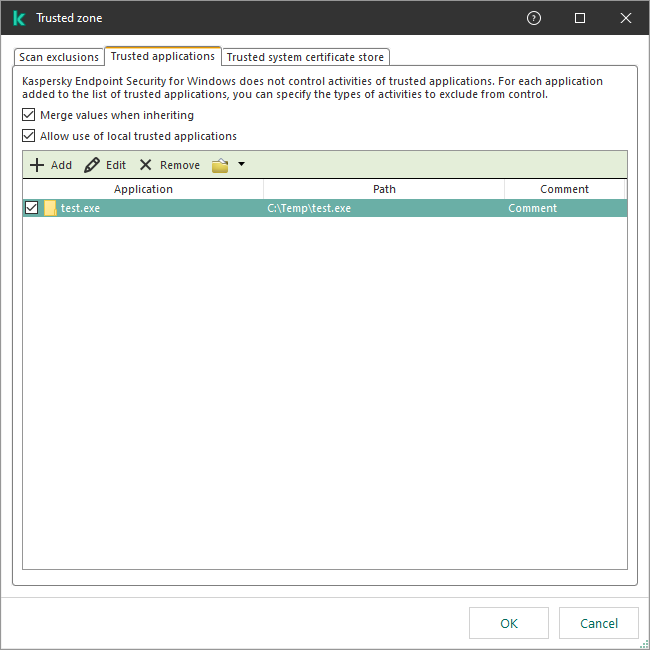
How to export and import the trusted zone in the Administration Console (MMC)
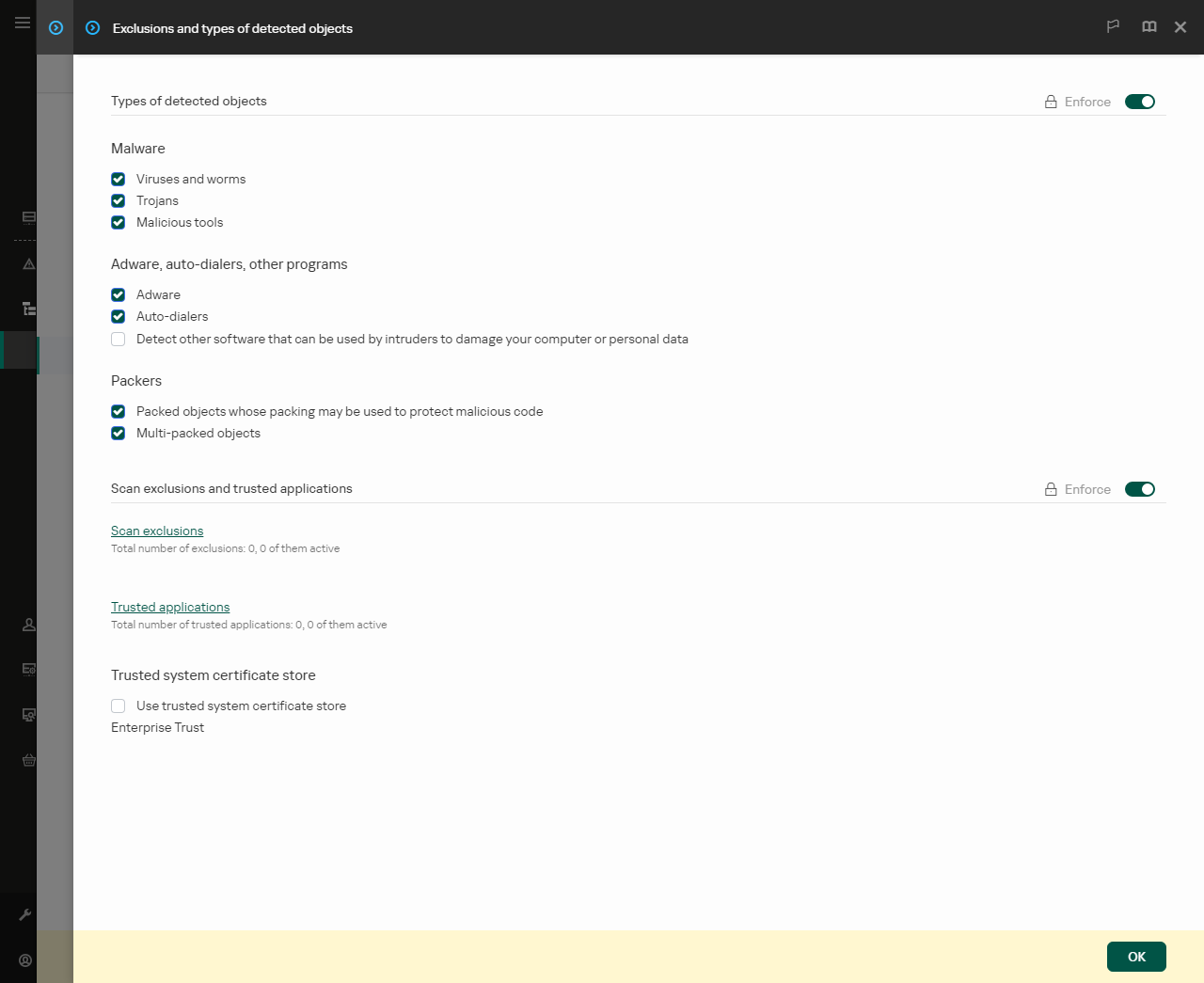
How to export or import the trusted zone in Web Console and Cloud Console
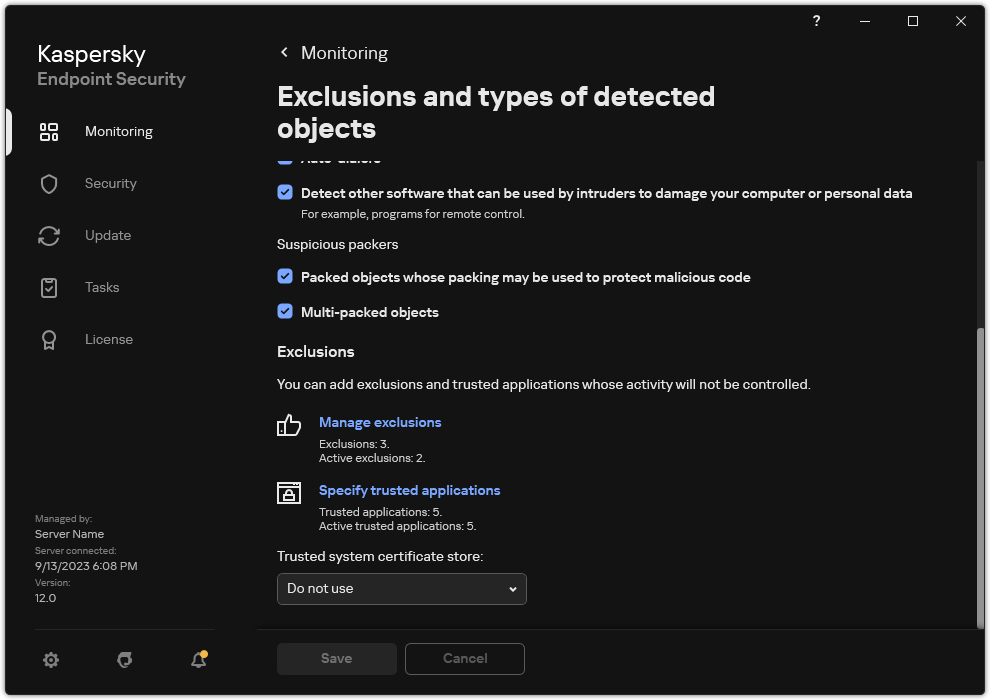
How to export or import the trusted zone in the application interface