Transmitting patches and installing updates in an isolated network
After you have finished configuring Administration Servers, you can transfer patches containing the required updates from the Administration Server with internet access to isolated Administration Servers. You can transmit and install updates as often as you need, for example, once or several times per day.
You need an external device, such as a removable drive, to transfer patches and the list of required updates between Administration Servers. Therefore, make sure that the external device has enough disk space for downloading and storing patches.
The process of transmitting patches and the list of required updates is shown in the figure and described below:
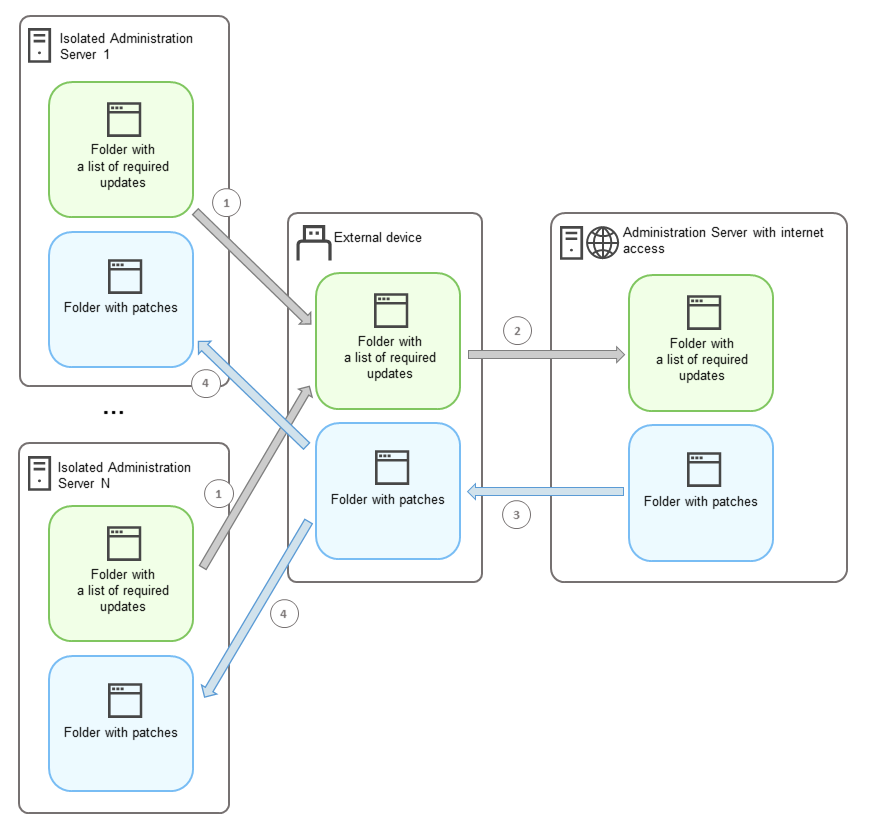
The process of transmitting patches and the list of required updates between the Administration Server with internet access and isolated Administration Servers
To install updates and fix vulnerabilities on managed devices connected to isolated Administration Servers:
- Start the Install required updates and fix vulnerabilities task if it is not yet running.
- Connect an external device to any isolated Administration Server.
- Create two folders on the external device: one for the list of required updates and one for patches. You can name these folders whatever you like.
If you created these folders earlier, clear them.
- Copy the list of required updates from every isolated Administration Server and paste this list into the folder for the list of required updates on the external device.
As a result, you unite all lists acquired from all isolated Administration Servers into one folder. This folder contains binary files with the IDs of patches required for all isolated Administration Servers.
- Connect the external device to the Administration Server with internet access.
- Copy the list of required updates from the external device and paste this list into the folder for the list of required updates on the Administration Server with internet access.
All required patches are automatically downloaded from the internet to the folder for patches on the Administration Server. This can take several hours.
- Make sure that all required patches are downloaded. For this purpose, you can do one of the following:
- Check the folder for patches on the Administration Server with internet access. All patches that were specified in the list of required updates should be downloaded to the necessary folder. This is more convenient if a small number of patches is required.
- Prepare a special script, for example, a shell script. If you get a large number of patches, this will be difficult to check on your own that all patches have been downloaded. In such cases, it is better to automate the check.
- Copy the patches from the Administration Server with internet access and paste them into the corresponding folder on your external device.
- Transfer the patches to every isolated Administration Server. Put the patches into a specific folder for them.
As a result, every isolated Administration Server creates an actual list of updates that are required for managed devices connected to the current Administration Server. After the Administration Server with internet access receives the list of required updates, the Administration Server downloads patches from the internet. When these patches appear on isolated Administration Servers, the Install required updates and fix vulnerabilities task handles the patches. Thus, updates are installed on managed devices and third-party software vulnerabilities are fixed.
When the Install required updates and fix vulnerabilities task is running, do not reboot the Administration Server device and do not run the Backup of Administration Server data task (it will also cause a reboot). As a result, the Install required updates and fix vulnerabilities task is interrupted, and updates are not installed. In this case, you have to restart this task manually or wait for the task to start according to the configured schedule.
