How to configure receiving Kaspersky CyberTrace events in Kaspersky Unified Monitoring and Analysis Platform
Show applications and versions that this article concerns
- Kaspersky CyberTrace 4.4
- Kaspersky CyberTrace 4.3
- Kaspersky CyberTrace 4.2
- Kaspersky Unified Monitoring and Analysis Platform 3.2
- Kaspersky Unified Monitoring and Analysis Platform 3.0.3
- Kaspersky Unified Monitoring and Analysis Platform 3.0.2
Configure receiving Kaspersky CyberTrace events in the Kaspersky Unified Monitoring and Analysis Platform (KUMA) SIEM system.
CyberTrace minimum system requirements
Kaspersky CyberTrace system requirements depend on the selected usage mode and the number of events processed per second (EPS). Below is a table with the minimum system requirements for the three most common modes.
| Usage mode | EPS | Number of CPU cores | RAM, GB | Disk space, GB | Network bandwidth,
Gbps |
|---|---|---|---|---|---|
| Evaluation mode | 250 | 4 | 16 | 468 | 1 |
| Multi-user mode with commercial feeds, no retroscan | 2,000 | 8 | 16 | 17 | 1 |
| Multi-user mode with commercial feeds and retroscan | 2,000 | 8 | 16 | 3,724 | 1 |
For system requirements for higher EPS values and descriptions of usage modes, see Online Help.
How to install CyberTrace on Linux
To install CyberTrace on Linux, use the RPM or DEB package.
- Extract the CyberTrace archive to a temporary directory:
- For the RPM package:
tar -C /opt -xvzf CyberTrace-rpm.tar.gz --no-same-owner
- For the DEB package:
tar -C /opt -xvzf CyberTrace-deb.tar.gz --no-same-owner
- For the RPM package:
- Navigate to the directory with the extracted files from the archive:
cd /opt/cybertrace
- Start the installation script:
./run.sh install
- Accept the EULA in the configurator that opens and wait for it to complete.
If the configurator cannot automatically determine the ports for the CyberTrace web interface and the Elastic database, specify them manually. - Log into the CyberTrace web interface.
Use the username admin and password CyberTrace!1 to access the pre-installed account.
How to configure CyberTrace
You can configure CyberTrace to integrate with KUMA immediately after the installation in the initial setup wizard or later in the web interface of the application.
How to configure CyberTrace in the initial setup wizard
- Wait for the wizard to open: it happens automatically when CyberTrace is started for the first time.
- Select KUMA in the select SIEM drop-down list and click Next to open the Connection Settings window.
- Select IP and port in the Service listens on toggle group.
- Enter the CyberTrace IP address in the IP address field in the Service listens on and Service sends events to field blocks.
- Fill in the values for the Port fields:
- 9999 in the Service listens on field block
- 9998 in the Service sends events to field block
- Click Next.
- Leave all fields blank in the Proxy Settings window that opens and click Next to open the Licensing Settings window.
- Add the CyberTrace license key to the Kaspersky CyberTrace license key field.
- Add a certificate that allows downloading data lists from update servers to the Kaspersky Threat Data Feeds certificate field and click Next.
How to configure CyberTrace via the web interface
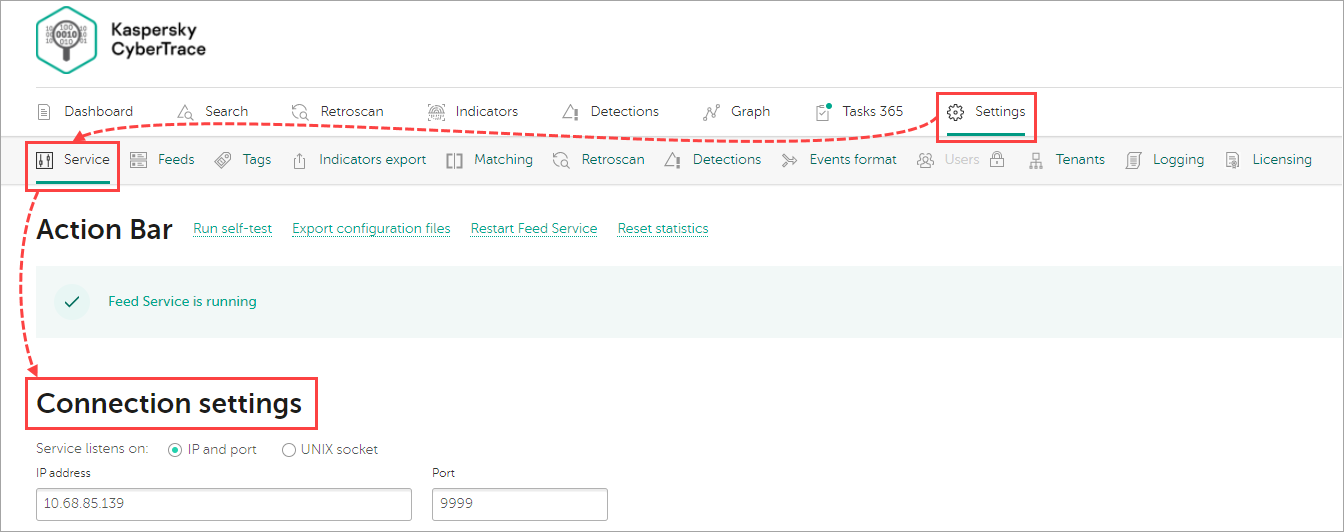
- Go to Settings → Service → Connection Settings.
- Select IP and port in the Service listens on toggle group.
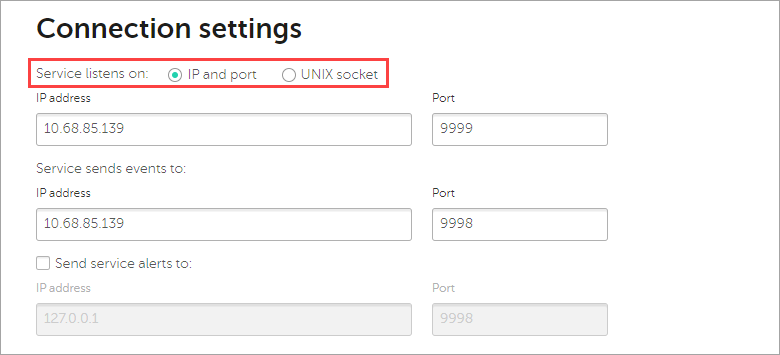
- Enter the CyberTrace IP address in the IP address field in the Service listens on and Service sends events to field blocks.
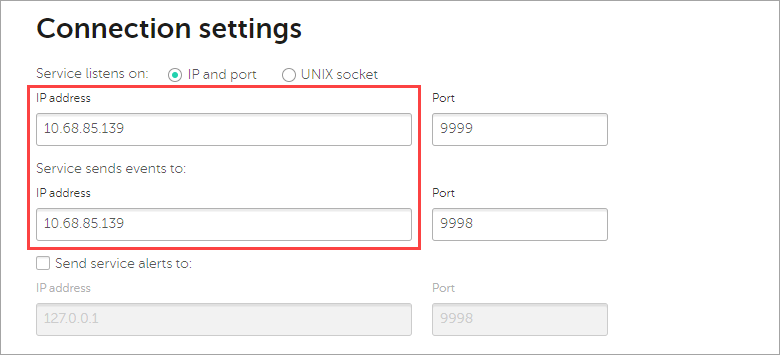
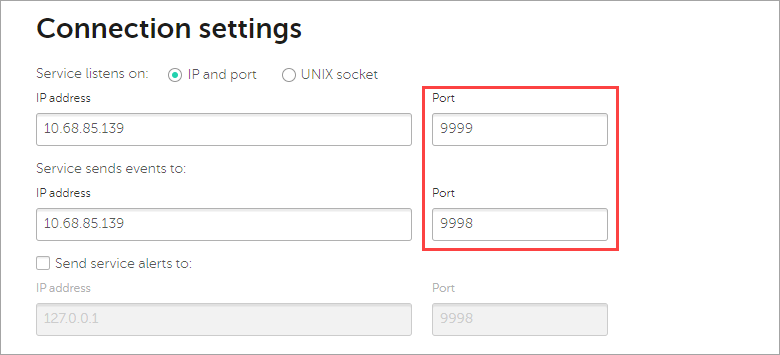
- Fill in the values for the Port fields:
- 9999 in the Service listens on field block
- 9998 in the Service sends events to field block
- Go to the Web interface block.
- Enter the CyberTrace IP address in the IP address or hostname field and click Save.
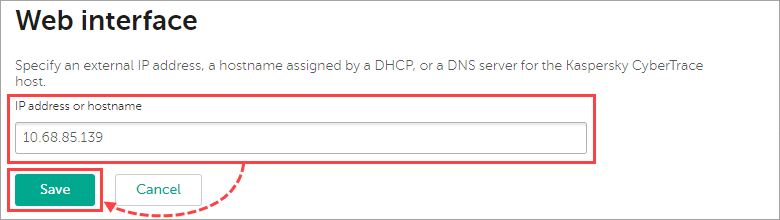
- Click Restart the CyberTrace Service in the upper toolbar.
How to configure KUMA
Create an event enrichment rule and bind it to a collector or correlator, then restart the services.
How to create an enrichment rule in KUMA
- Go to the Resources section and select Enrichment rules.
- Select the required folder and click Add.
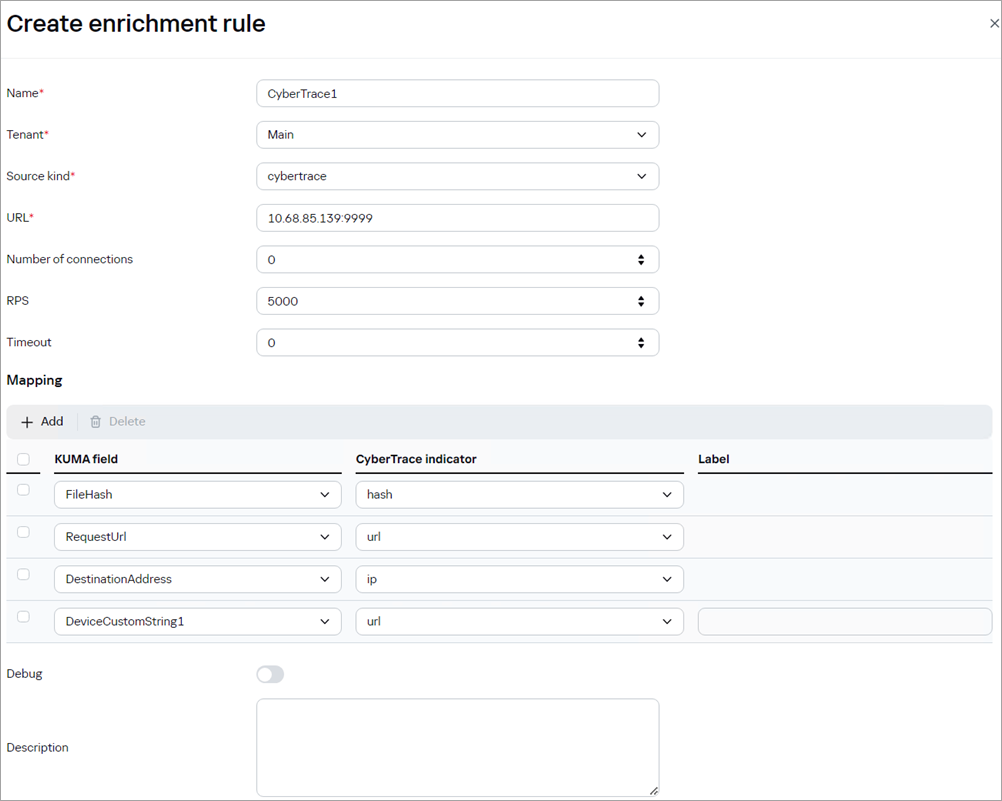
- Fill in the required fields:
- Name: any unique name of a rule.
- Tenant: select the required value from the drop-down list, by default — Main.
- Source kind: cybertrace.
- URL: <IP address CyberTrace>:9999. For example: 10.68.85.139:9999.
- Number of connections: fill in if necessary, by default — 0.
- RPS: 5000.
- Timeout: fill in if necessary, by default — 0.
- Mapping:
- FileHash — hash;
- RequestUrl — url;
- DestinationAddress — ip;
- DeviceCustomString1 — url.
- Debug: disabled by default.
- Description: fill in if necessary or leave the field blank.
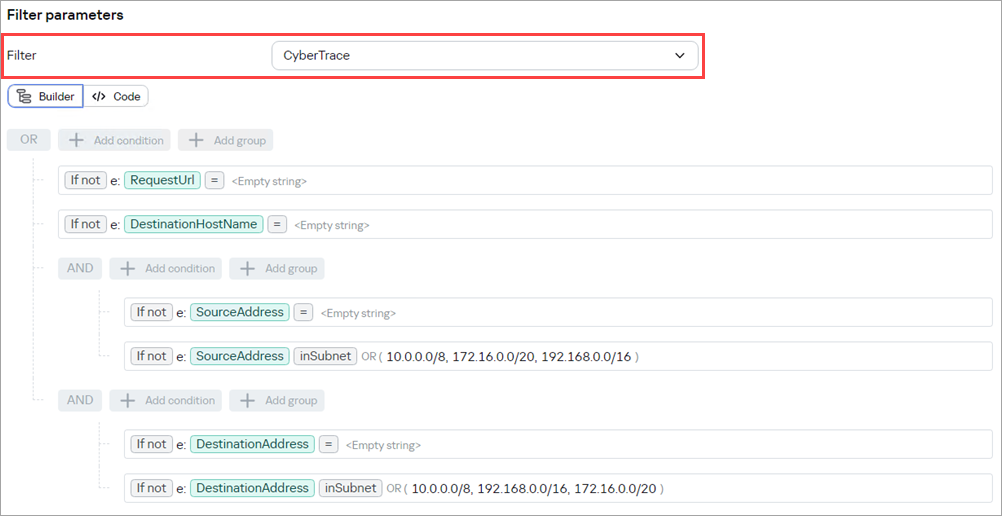
- Select or create a filter if you want to reduce the load on CyberTrace.
- Click Save.
How to bind an enrichment rule to a collector or correlator and restart services in KUMA
- Go to the Resources section and select Collectors or Correlators.
- Select the collector or correlator that you want to enrich with data from CyberTrace.
- Go to Event enrichment for a collector or Enrichment for a correlator and click Add enrichment.
- In the Enrichment rule field, select the required enrichment rule from the drop-down list.
- Go to the Setup validation section and click Save and restart services.
- Click Save.
How to test CyberTrace integration with KUMA
By default, the connection to CyberTrace is not checked in KUMA. You can manually check the integration with CyberTrace and ensure that event enrichment is performed:
- Open the command line.
- Send a request to the collector, which will trigger an event and the following enrichment. You can use http://malware.example.com as a test URL. Example query:
curl --request POST \
--url http://<IP address of the device on which the collector is installed>:<collector port>/input \
--header 'Content-Type: application/json' \
--data '{"RequestUrl":"http://malware.example.com"}' - Open KUMA and go to the Events section.
- Find the enriched event that was created. Example of a search query:
SELECT * FROM `events` WHERE RequestUrl = 'http://malware.example.com' ORDER BY Timestamp DESC LIMIT 250
- Open the properties of the found event and check that it contains the TI indicator and indicator category with CyberTrace data.
